Difference between revisions of "Policy:Ping Response Policy Page"
(Initial page) |
(No difference)
|
Revision as of 17:41, 10 November 2021
Home > Using > Web User Interface > Views > Ping response policy
Contents
1 Overview
A policy is an instructions run on one or more of your monitored servers looking for an event that could lead to loss of, or disruption to, an organisation's operations, services or functions. Each policy is found in an application
A policy is represented in Veloopti by the policy icon: ![]()
The 'Ping response' policy enables you to ??? The command may contain arguments.
Ping response policies must be added to a Policy Group for automated deployment onto one or more managed nodes.
1.1 Creating or editing a policy
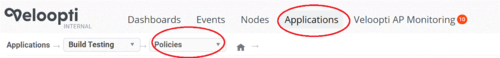
Ping Response policies are created and edited from within an application. A policy is only visible from within the application that it was created in. After entering an application select 'Policies' from the application breadcrumb to view the .
- Click on the Application menu item
- Click on the Application
- Select the Policies breadcrumb as shown below to view the Policy view
- From here you can either click on the Policy Wizard to create a new Policy or select a ping Response policy to modify it.
Tabs run down the left hand side of the view. Clicking on a tab will change the page that allows for a particular part of the policy to be modified. They are: Overview, Attributes, Conditions, Node Overrides, Schedule, Audit Log and View Data.
2.1 Ping Response Policy Page
NAME The title of the policy that can be used to tell the policy apart from others
DESCRIPTION Describes the policy and explains what it does
TYPE Ping Response
NODE OVERRIDES CONDITIONS Enabling this slider makes the Node Overrides tab visible.
2.2 Attributes
EXECUTABLE The full path (including the binary) of the executable to run. Don't include arguments here, there is a separate field for that below
INITIAL DIRECTORY Also known as the current working directory, this is a location in your filesystem to start running the executable from. This can help the executable/script to find any configuration or other files that need to reside in the same file location as itself.
ARGUMENTS The parameters that are given after the name of the program are known as Command Line Arguments. Veloopti provides a way of passing these to the executable/script.
- VALUE
- If there are more than one argument then they are joined together separated by a space character.
ENVIRONMENTAL VARIABLES Veloopti can add an environment variable that may be used by the program as as a part of the standard environment variable set. Once the program completed the environment variable ceases to be available.
- NAME The name of the variable. This is the part that appears before the =
- VALUE The value of the variable. This is the part that appears after the =
2.3 Conditions
Click on the 'add' button to the right to add a condition rule. The rules may be moved up and down by clicking on the rule changing its position. Click on the [Add] button to bring up the dialogue to add a condition to the policy.
NOTE: Currently changing the position of order of the rules does not do anything as they are evaluated in order of severity.
SEVERITY The severity that appears on the event that is raised by a threshold violation of the rule
EVENT SHORT DESCRIPTION The short event description that appears on the event that is raised
- EVALUATE
Either add a new row by clicking on the [Add] button or click on an existing row to enter the edit condition dialogue box.
- Metric Select a metric upon which to perform a threshold evaluation. The options available are:
- Standard Out (text)
- Standard Out (Number)
- Error Out
- Exit Code
- Run Duration (seconds)
- Timed out
- Metric Select a metric upon which to perform a threshold evaluation. The options available are:
- OperatorSelect an operator to perform against the Metric above. Different options are available for different metrics.
- Equals
- Contains
- Doesn't Contain
- Does not equal
- Regular Expression Match
- Regular Expression Suppress Matches
- OperatorSelect an operator to perform against the Metric above. Different options are available for different metrics.
- Value Enter a value to compare the metric against using the operator.
- BREACH AND RESET
- Breach duration Enter the number of consecutive breaches that need to occur for an event to be raised
- BREACH AND RESET
- Reset Duration Enter the number of consecutive reset conditions, the number that the metric must be (usually) below, for the event severity to be set to Normal
- CREATE EVENT
- Event Severity The severity that appears on the event that is raised by a threshold violation of the rule
- Event Short Description The short event description that appears on the event that is raised
- Event Long Description The long description that appears in the event
- Auto Action Select an action to run automatically when the condition of raising an event is met.
- Close event if auto action runs successfully If the auto actions runs successfully then the event will be closed.
- This check box closes the event if the command exits with a successful 'error code'.
- For instance, the ping command on a Mac returns an error code of 0 for success and 2 for a ping failure.
- And the ping command on a windows OS in a command prompt returns 0 for success and 1 for failure.
- Close event if auto action runs successfully If the auto actions runs successfully then the event will be closed.
- On Windows, after running the command, run the below command to see the error code that the command exited with
-
C:\users\Muuss\echo %ERRORLEVEL%
- EVENT ACTIONS These actions are available to be run by any user that has the "Run Action from Event" permission. Unlike normal actions it does not rely on the Action "Level" permission of Operator, Power User or Administrator
- HELP TEXT This text appears on the event in the "Help" section.
- NOTIFICATION WORKFLOW Select the Notification Workflow that will be used for notifications and escalations.
2.4 Node Overrides
One policy can run on multiple nodes using the same conditions to create events. Individual nodes may require different threshold values in these conditions for effective monitoring. This is known as a "Node override condition".
This is currently not enabled.
2.5 Schedule
TYPE
- Basic Run the policy once per minute or once per hour
- Time of day Run the policy once her day
- Custom Run the policy on a complex schedule
EVERY
- Basic Select "Minutes" or "Hours" and type when on the minute or hour the policy should run.
- Time of day Select hour and minute and the weekday(s) that the policy should run.
- Custom Select "Minutes" or "Hours" and type when on the minute or hour the policy should run. Select the time range when the policy should be active: e.g. 9:00am - 5:00pm. Welect the weekday(s) that the policy should run on.
2.6 Audit Log
DATE/TIME The date/time that the audit event occurred
USER The user that initiated the audited event
EVENT A description of what happened to the policy. Blue text indicates that it is a link to the described item.
ACTION If an action is available for the audit item it can be initiated here. For instance, roll back the policy to the previous version or restore the accidentally deleted policy.
2.7 View Data
SELECT YOUR NODE Use the drop down list box to select the node that it is deployed to. Graphs will then be visible in the below space that contains the metrics that have been collected over the last hour.
NOTE: Only nodes with this policy currently deployed are able to be selected.